The conflict in Iran continues, and as a result, shipping through the Strait of Hormuz remains largely suspended, with the flow of ships through the strategic waterway slowing to a trickle. While it is undisputed that Iran’s ability to launch attacks has not been eliminated (as of this writing), Iran’s attacks, both by missile and by drone, have declined from a veritable deluge in the first days of the conflict
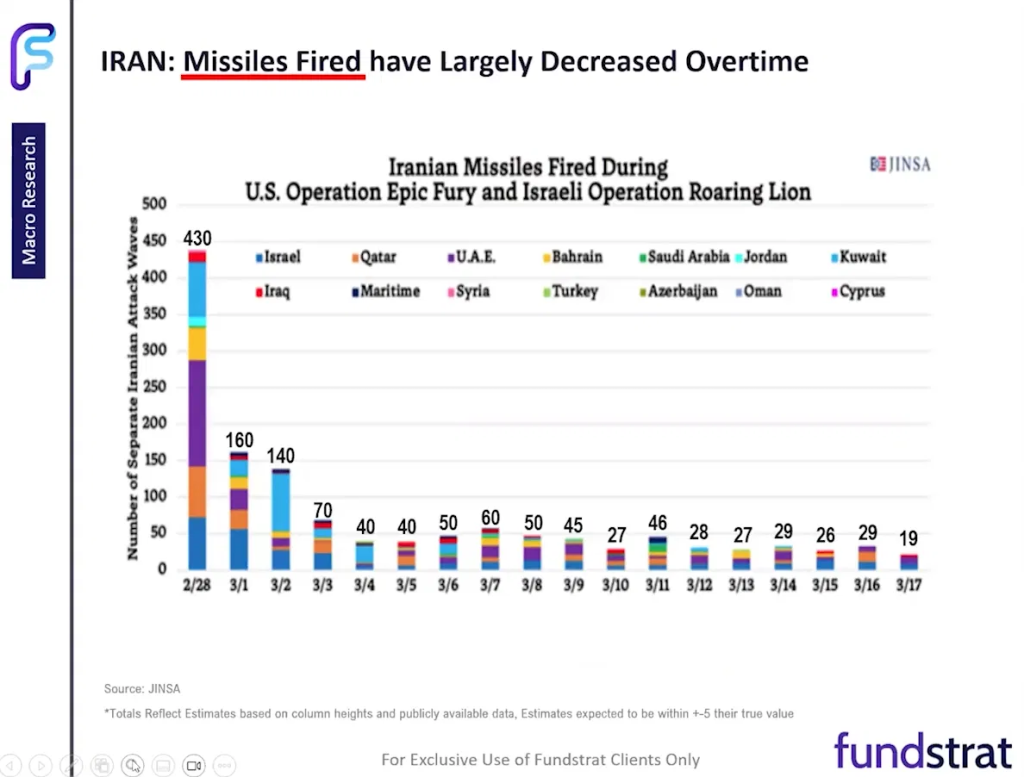
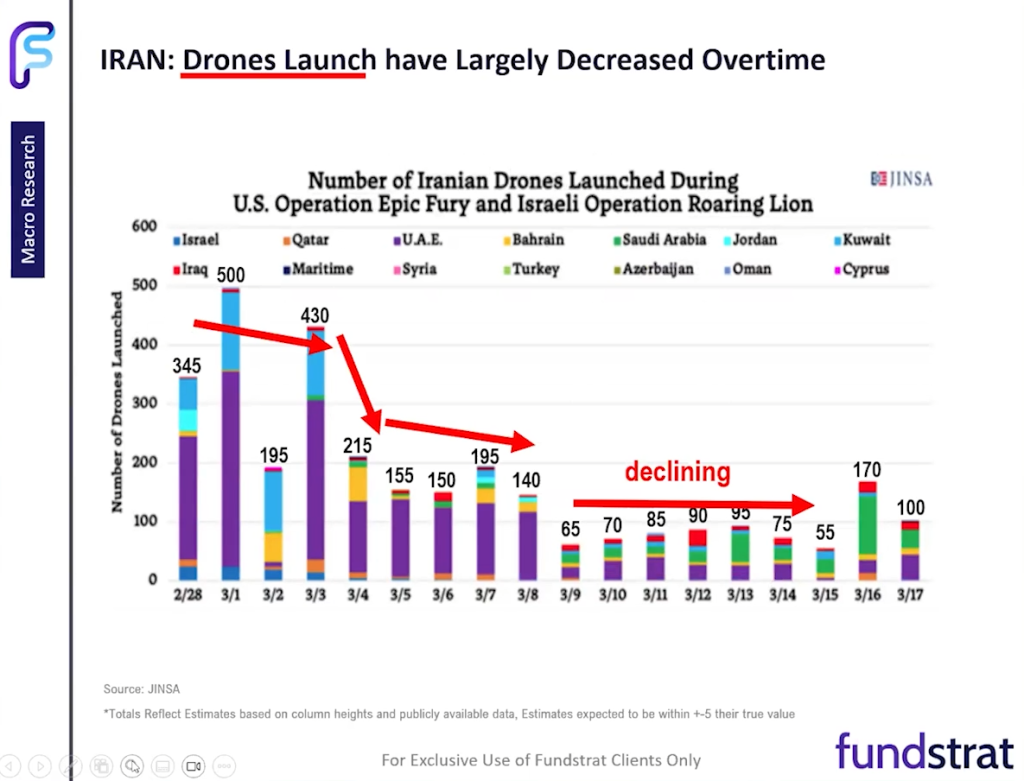
It’s not clear whether this is due to diminished capacity, a tactical decision to launch more judiciously, or some other reason. For ship owners, it might not matter which it is. They remain reluctant to send their ships through the waterway. This reluctance remains even though President Trump has offered to provide such ships with military escorts, exhorting owners to “show some guts” and ignore the risks.
Their continued wariness is likely due to skepticism that Trump’s proposals sufficiently reduce the risk of attack. Erik Hånell, chief executive of oil-tanker company Stena Bulk, expressed doubts both about whether the military escorts will materialize and about how much good they will do. Speaking with the Financial Times, he opined that “the promise that we can go [be escorted through the strait], I don’t see that happening any time soon,” adding that even naval escorts from the U.S. and/or its allies “simply cannot guarantee secure passage, not even close to secured passage, at this stage.”
Even those so inclined to risk crews, ships, and cargo are likely constrained by their insurance companies. Although it’s hardly a secret, it’s easy to forget how strong an influence insurance-company decisions and assessments have on decisions in every aspect of business (and life). For instance, companies seeking to build data centers are increasingly running up against resistance from lenders who demand that the proposed projects be fully covered – and as Kimberly McGrath, a partner partner specializing in data-center financing at law firm Kirkland & Ellis, told the Financial Times recently, “At this scale, insurance either isn’t available in the market, or it’s just prohibitively expensive.”
The maritime-shipping industry is largely governed by eye-crossingly intricate coverage charts, with each ship covered by a complex web of policies from various insurers – policies that govern, in minute detail, what kinds of loss events are covered, for how much, and by whom. Some types of losses end up being covered by multiple policies, which often means long, attorney-driven arguments between insurers as to who has to pay up first whenever something goes wrong.
What most cargo-ship insurance policies have in common is that they typically exclude losses that happen in the context of war or similar circumstances involving military hostilities of a geopolitical nature. Though modern military conflicts, such as the current one in Iran, often take place without a formal declaration of war, war-risk policies cover losses caused by weapons of war, whether in undeclared wars/hostilities between sovereign nations, civil wars/rebellions, or during some acts of piracy (state-sponsored piracy, for example). War-risk policies cover damage and destruction, as well as losses arising from loss of access (for instance, a ship trapped in hostile territory or otherwise seized).
Importantly, war-risk policies are typically issued on a per-voyage basis and can be revoked on very short notice. This almost certainly factors into shipowners’ decisions about the Strait of Hormuz or the Middle East in general. Some contemporary news outlets report war-risk coverage rising from roughly 0.5% of the vessel’s value (per voyage) to as much as 7% – a 14-fold increase, and that’s for those insurers still willing to provide coverage. This is a big reason why President Trump’s idea of providing U.S. Navy escorts to tankers through the strait had few takers.
A further offer from the White House to provide $20 billion of reinsurance (with Chubb CB 0.38% as a lead partner in the effort) to coverage providers does not seem to have improved matters all that much, if oil prices are any indication, and that is perhaps because in addition to war risk, owners need to worry about liability: a successful attack could result in their being held responsible for damages resulting from the subsequent massive oil spill, after all.
As an aside, for those anxiously awaiting the full resumption of oil shipments, it’s worth remembering that tankers also need to pass through the Red Sea, where they have previously been attacked by Houthis allied with Iran.
Cyberattack risk
While the situation regarding oceanic oil shipping remains unresolved, there is arguably a constructive case to be made for investors looking for opportunity, and that’s in cybersecurity. Along with China, Russia, and North Korea, Iran has long been widely regarded as one of the “Big Four” of state-sponsored cyberattack threats, not the least because among the four nations, Iran’s hackers are arguably some of the most aggressive and nimble.
In the past, Iranian hackers have been blamed (or taken credit for) attacks that include:
- A 2013 Distributed Denial of Service attack on financial institutions that cost an estimated $100 million in damages to the likes of JPMorgan Chase, Wells Fargo, and American Express
- The 2012 “Shamoon” attack that forced Saudi Aramco to take its network completely offline for a week (full restoration took months)
- A 2014 attack on the Sands Casino Las Vegas (in response to remarks made by the late Sheldon Adelson, then chairman/chief executive of Sands)
In the public sector, perhaps Iran’s biggest cyberattack success came in the form of 2014’s Operation Cleaver, which compromised 50 private- and public-sector entities in 16 countries, reportedly including:
- U.S. Navy and Marine Corps
- Saudi Aramco
- Petroleos Mexicanos
- Qatar Airways
- Korean Air
Though their identities remain non-disclosed, the attack also compromised various U.S. companies in the automotive, airline, defense and aerospace industries, as well as several major research institutions.
Most recently, Iran successfully carried out a March 11 attack on Stryker SYK -1.10% , a major medtech company and defense contractor whose products include medical tools, orthopedic implants, and hospital equipment such as ambulance-communication systems, defibrillators, beds, and stretchers. (Stryker shares fell as much as 7.6% after the attack, and the company’s systems have yet to be fully restored as of this writing.)
It is, therefore, not much of a leap to theorize that Iran is at least considering further cyberattacks as the military conflict continues, and that the threat should not be disregarded.
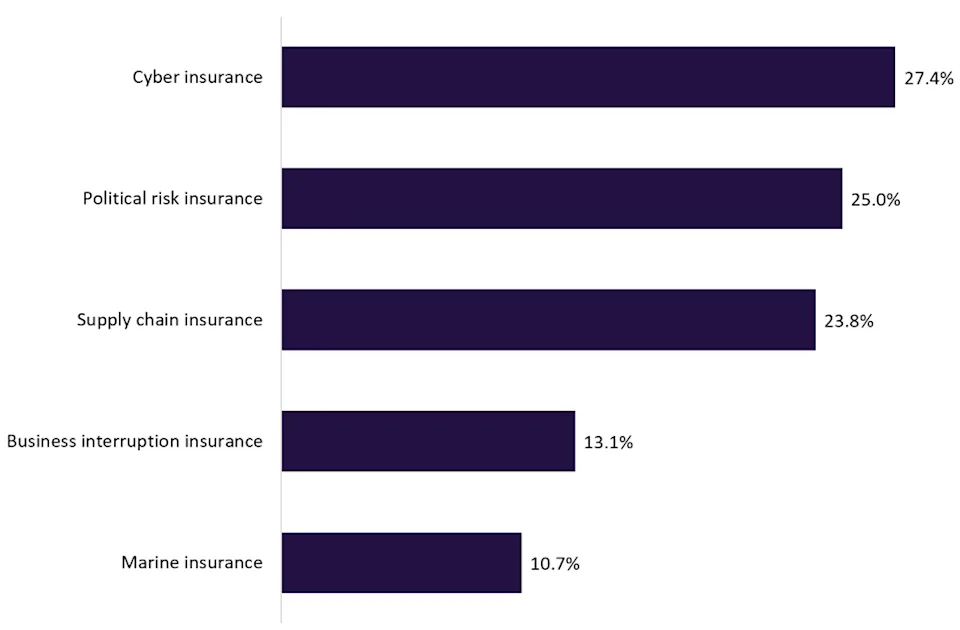
Reflexively, many companies and organizations might be eyeing cyber insurance. Indeed, in a GlobalData poll of insurance industry professionals last fall, nearly a third of respondents viewed cyber-insurance demand as being the most likely to increase as geopolitical tensions, especially tensions involving the U.S., Israel, and Iran – ranking it above supply chain insurance and far above marine insurance. GlobalData analyst Charlie Hutcherson suggested that this is consistent with a growing business perception that military hostilities could be accompanied by “a conflict spillover into Western markets through cyber activity.”
The demand for cybersecurity, regardless of insurance
As Aaron Le Marquer, head of policyholder disputes at law firm Stewarts, notes, “the warning of potential Iranian cyberattacks is particularly worrying even for those businesses who carry comprehensive cyber insurance.” That’s because it’s standard practice for cyber insurance policies to exclude acts of war. In fact, Lloyds has seven categories of such exclusions, ranging from a coverage that completely excludes losses from state-backed attacks to those that provide coverage based on whether a war-like scenario is in force, and the extent and type of losses incurred.
It’s worth noting that with regard to war, cyberinsurance policies have not really been tested. There is a relative lack of legal precedent regarding what counts as a state-backed attack and specifically what counts as a war-related state-backed attack. So even companies that err on the side of caution in attempting to obtain coverage of war-related cyber attacks run the risk of incurring losses.
Even if the U.S. and Israel are successful in disrupting Iran’s power and data infrastructure, the threat could well remain: Iran’s cyberwarfare operations are decentralized and operate from around the world, making it possible for attacks to continue even if the country itself ends up being largely subdued and brought under control.
As the cybersecurity newsletter The Register reports, Iranian hackers began breaching networks of key players in banking, software, and infrastructure in February, likely anticipating the likelihood of full-on conflict. That means the possible indirect compromise of networks in the defense and aerospace sectors.
If we assume that many businesses are aware of both the heightened cyberattack risk and the uncertainties that remain even after acquiring cyber insurance, we can see our way toward a constructive argument for increased demand for cybersecurity products and services. The demand is reinforced by covenants in cyber insurance that require certain safeguards be put in place before agreeing to provide coverage (think of it as similar to insurers requiring homeowners to install smoke detectors before agreeing to underwrite coverage).
For the style of cyberattacks that many cybersecurity experts believe Iran is likely to attempt, there are a few types of cybersecurity:
Endpoint Detection and Response (EDR) and Managed Detection and Response (MDR)
EDR involves the constant monitoring of computers and services to detect and respond to threats as they emerge. MDR involves augmenting EDR with third-party human experts to make defense more proactive and effective. Leading providers of EDR and MDR include:
- Crowdstrike CRWD -4.06% . Many in the industry consider CrowdStrike’s Falcon MDR/EDR offering to be the gold standard in this area. For certain tiers of service, CRWD offers a $1 million breach prevention warranty.
- SentinelOne S -8.21% . SentinelOne’s EDR features a “Rollback” feature that helps restore networks to a previous healthy state if an attack is detected. The company also claims that their AI-driven Vigilance MDR platform provides faster response times.
- Palo Alto Networks PANW -4.22% . Palo Alto’s MDR service, Unit 42 is widely respected in the industry, and the team’s malware analysis reports and threat observations are closely followed by other security experts.
Identity Validation
If we assume that The Register report is accurate, zero-trust solutions – those designed to operate on the assumption that a given system has already somehow been breached even if the specifics of the breach remain unknown – also will become important. A key component of zero-trust architecture, which as an aside is an ongoing priority for the Department of Defense, is identity validation. This includes familiar services like multi-factor authentication and the replacement of VPNs with Zero Trust Network Access (ZTNA) architecture. Leading providers include
- Zscaler ZS -6.81% . Zero trust implementation is Zscaler’s primary offering, with a decentralized Zero Trust Exchange security cloud that connects users to applications rather than networks.
- Okta OKTA -5.62% . Okta’s identity validation offering focuses on monitoring users to ensure that each user gets only the minimum of what is required and only for as long as it’s required. The company claims that its AI-driven identity threat protection helps detect attacks more quickly.
- Cloudflare NET -2.23% . One of Cloudflare’s specialties is helping companies transition from VPNs, which are regarded as less secure, to ZTNA. They are also one of the leaders in integrating post-quantum cryptography into their offerings.
Palo Alto Networks also has a well-regarded suite of offerings in this area.
Resilience and Backup Solutions.
As Stryker and Saudi Aramco can each confirm, a hallmark of Iranian hackers is the use of “wiper” tactics (including but not limited to malware) to destroy data and render systems inoperable. The main safeguard against such attacks are “immutable” backups – periodic backups, ideally offsite, that are locked for specific durations so they cannot be altered or deleted – sort of like the time-delay locks used by banks on their safes. Leading providers of such backups include
- Rubrik RBRK -4.63% . Rubrik specializes in zero-trust security, and its backup offerings use the company’s “Atlas” proprietary file format. Atlas, by default, renders backups immutable and unalterable simply by virtue of making it impossible to overwrite a file. In effect, this means that backups made before an attack cannot be altered, so there is minimal risk of accidentally restoring a version that was infected.
- Commvault CVLT -2.78% . Commvault’s backup platform includes both cloud-based and air-gapped options, as well as the option for dual-authorization locks that increase security by requiring authorization from two separate humans to change any retention/backup policies and practices.
Conclusion
An analysis of how we got here in the geopolitical sense is far beyond the scope of this note, and we will certainly not try to assess how much of our current situation was planned and how much was happenstance. After all, as Prussian strategist Helmuth von Moltke noted, “no plan survives first contact with the enemy.” (Generals Dwight D. Eisenhower and George S. Patton are reported to have echoed similar sentiments.)
What does seem clear is that while the Iran conflict has presented investors with many challenges, there arguably remain pockets of potential opportunity that are worth researching. In our view, cybersecurity is one such possibility.
However, as always, Signal From Noise should not be used as a source of investment recommendations but rather ideas for further investigation. We encourage you to explore our full Signal From Noise library, which includes deep dives on the recent gold rush, quantum computing, and the race to onshore chip fabrication. You can also find our take on space-exploration investments, a recent update on AI focusing on sovereign AI and AI agents, and the rising wealth of women.









